Anyone holding an insignificant amount of bitcoins should consider multisignature security, including ways to mitigate potential attacks.
This is an opinion editorial by Anant Tapadia, a computer engineer and contributor to the Bitcoin custody project. Bitcoin Keeper and Wallet Hexa Kab.
Multisignature security, or “multisig,” offers more security guarantees than single-signature (singlesig) solutions. While I believe that singlesig is a good form of holding when one is just starting out with bitcoins or managing a small amount, in my opinion, anyone holding insignificant amounts of bitcoins for the long term should evaluate the multisig option.

Define Multisig
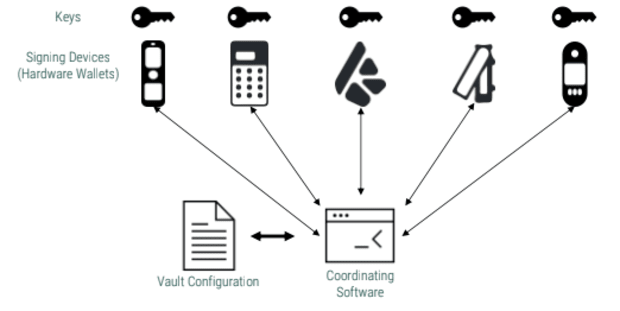
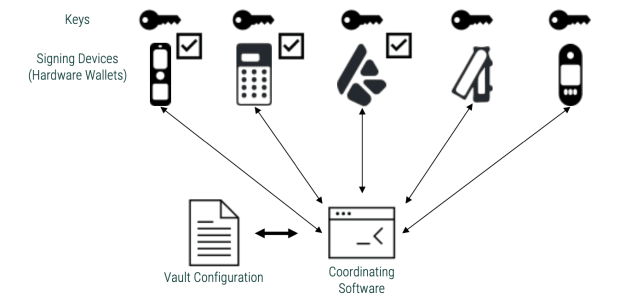
It’s important to understand what “wallet” means before I lay out the case for one type versus the other. Multisig wallets are referred to as “vaults” in applications like Bitcoin Keeper and Blue Wallet, while some also refer to them as “coordinators” or “coordinating software.” It’s basically a wallet that can talk to multiple signing devices and coordinate between them for incoming transactions (mostly using the PSBT format). In comparison, the singlesig wallet only talks to one token. Singlesig wallets are also often tokenized, meaning the key is hot.
So, the apparent attack surface for singlesig and vault wallets is the same because they both play the same role. Having an alert device in both cases increases security and introduces a new attack surface.
Multisig is often referred to as “m-of-n,” where you need to “m key out of n” to enter the transaction. The output descriptor or bitcoin secure multisig setup (BSMS) is a format used to define a multisig configuration. This can be used to recreate the setup on another coordinator or to register multisig with the signature device.
Considerations For Holding Bitcoin

Minimizing Trust
The obvious advantage of having multiple alerts is that it reduces points of failure and adds redundancy to your setup. With the help of common examples of attacks on multisig included below, I will explain what attacks are applicable, even with singlesig held. However, with multisig, you can minimize the trust in one entity because many entities are involved.
Operational Efforts
Setting up and using multisig can be more operational time consuming and include other pitfalls if not done correctly. Therefore, I recommend that users only consider multisig for long-term HODLing, where regular transactions are not anticipated.
Setup Fees
A robust multi-vendor multisig (such as a three- to five-custody one) can be had for anywhere between $250 and $600. So, if you have about 0.5 BTC (about $11,000 at the time of writing this piece), spending less than 10% to secure it is not a bad idea, because the value of this bitcoin can appreciate very quickly.
The cost of signing devices is also reduced, for example, Tapsigner from Coinkite. Plus, using non-hardware-based soft keys provides a zero-cost option, but it is not recommended that this is used for more than one key in a multisig setup.
Common Attack Mitigation
Now I will look at some of the attacks that can occur if the prisoner key coordinator tries to do something bad. Then, I will explain how this is no different from the threat in a singlesig setup and what multisig wallets can do to reduce the risk. The ultimate responsibility rests with the user to ensure that they take the appropriate steps, as suggested below.
Wrong Received Address
The most direct attack I will outline is one where the user tries to receive funds, and the coordinator app shows the address of the attacker instead. In these scenarios, the software can still show that funds are received where the user intended. This attack is theoretically possible with a singlesig wallet because users rely on the wallet to generate addresses for them. There is no way to manually retrieve the address from your 12 or 24 word recovery phrase.
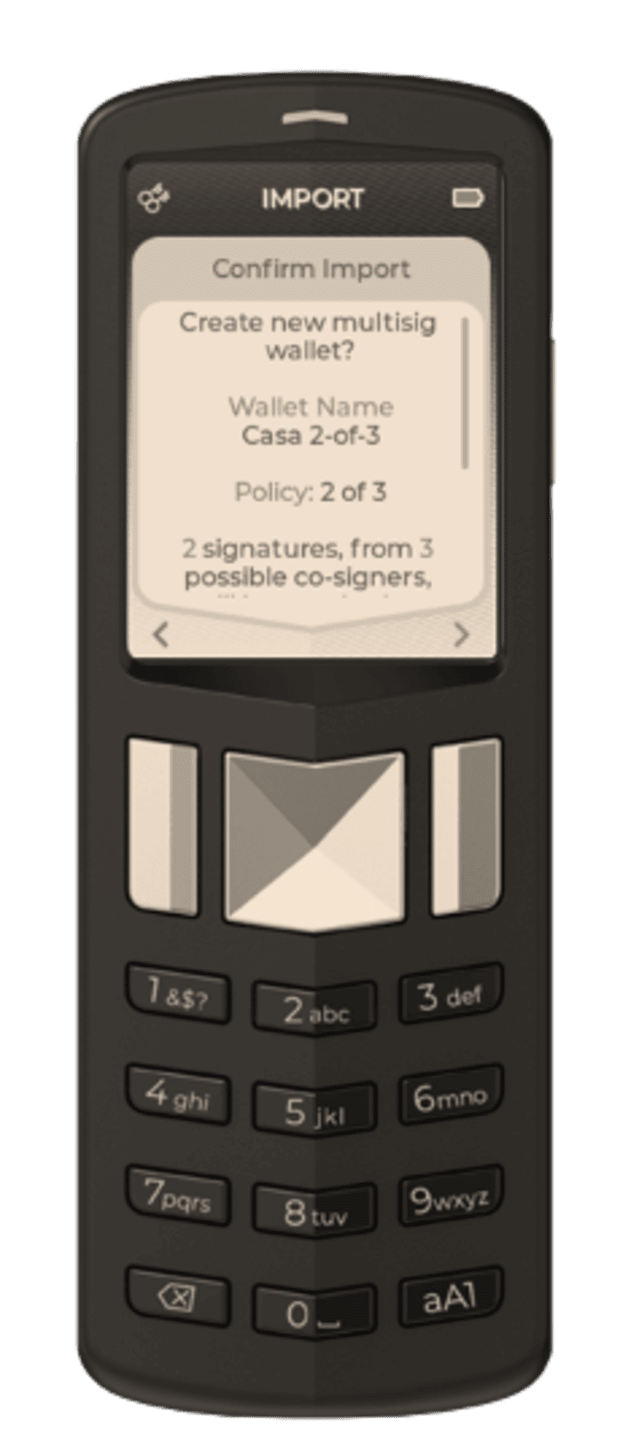
In the case of multisig wallets, this can be mitigated by checking the address on the signature device where the multisig is registered. You can also use other coordination software, import the same configuration and check the address that way.
Change the Send-To Address
As in the previous attack scenario, the multisig coordinator can change the address it is trying to send funds to when building the PSBT. The situation will be no different in the case of a regular singlesig wallet.
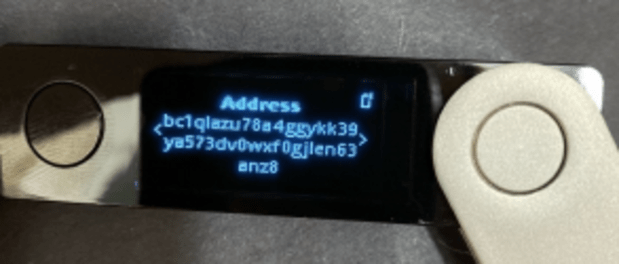
To reduce this risk, users are always advised to check the address on the alert device. Since the signing device enters the transaction containing the recipient’s address (in PSBT format), it will show the signed address. Unless there is some collusion between the coordinator app and the signing device, this is the best way to minimize trust in either of them.
Change Address Change
A less obvious attack is the coordinator application changing the address change in your transaction. This means that changes from the transaction will go to the attacker’s address. Unlike the send address, users may not check the change address when sending funds, making this attack less obvious. Again, there is no difference when it comes to the singlesig solution.
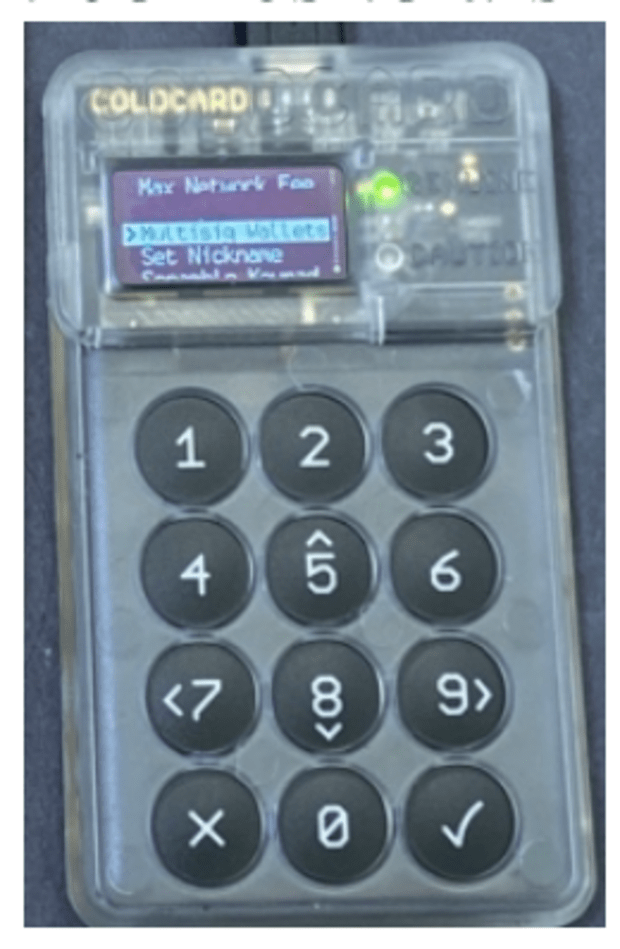
This is where multisig registration on the signature device is greatly needed. If the registration is completed, the signature device will not enter the transaction if it does not recognize the change address.
Change Registration
As the coordinator also coordinates the registration steps, different multisigs can be registered so that an attacker can control “n” or more keys. In this case, the alert device will not be able to recognize the receiving address or change the address correctly. The user will see the same address (the attacker) received on the signing device, and the change address will be correctly forwarded by the signing device because there is no way to confirm whether the other cosigner has changed or not.
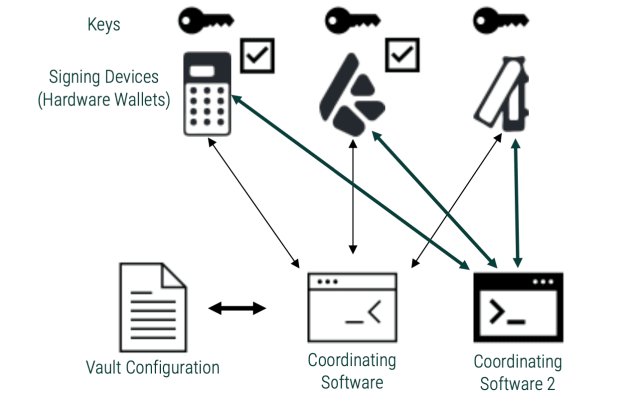
Therefore it is recommended to have a device listed “n” in your setup. In addition, you confirm the setup details on all these devices during registration. Another way to verify the correct registration is to set up the same multisig in another coordinator software and make sure it shows the correct details.
So, you can have a multisig with one register vault signature device and two blind signatures. Repeat the same process with other coordinators. Now, check the configuration on the multisig-registering coordinator and signature device. You can add other coordinators to the mix to eliminate collusion.
Ransom attack
This type of attack is similar to the one mentioned above, but the attacker controls less than the “n” key, so they cannot control the funds. But in a situation where you lose some keys, attackers can hold you to ransom, because now you don’t have the required minimum quorum. This attack can also be done by inserting a key, where an additional cosigner is added to the setup. This has the same effect as replacing multiple cosigners.
Again, checking cosigner details in various coordinators that require registration will reduce the likelihood of such an attack.
Using Multisig Custody For Your Bitcoin
To repeat: Having a minimum quorum of multisig signing devices and checking transaction details (when you need to make them) would be a good rule of thumb when using multisig.
When checking addresses or vault setup details, don’t just check the beginning and end of a string, because attackers can have strings that look the same.
Making sure the app is open source and checking the code (if you can) is also good for some. Support for common standards like BSMS and PSBT ensures that multisig setups or transactions can be transferred to other applications for verification.
I also believe that one can never go wrong with the testing setup. Once you have the multisig ready, duplicate the setup on another coordinator. Receive a small amount in one app and send a portion from another. Make sure the balance is properly applied to all coordinators after each step.
References and further reading:
- “The 10x Security Bitcoin Guide”
- “How Almost All Private Hardware Wallet Multisig Setups Are Insecure”
This is a guest post by Anant Tapadia. Opinions expressed are entirely their own and do not necessarily reflect those of BTC Inc or Bitcoin Magazine.